What Is Email Spoofing?
Basically, email spoofing is when a hacker changes the sender info to make it look like the message came from someone trustworthy, like a friend or a well-known company.
Email spoofing falls under the broader category of domain spoofing, where attackers attempt to fake a website name or email address, often as part of phishing attacks. Domain spoofing can extend beyond email to create fake websites or fraudulent advertisements.
But how does email spoofing differ from regular email fraud? While both aim to deceive recipients, email spoofing specifically focuses on falsifying the "From" field and other header details.
Imagine receiving an email that looks like it came from your bank, complete with official logos and language – but upon closer look, the email address might be slightly off (e.g., support @bank-example.com instead of support @bankexample.com). Regular email fraud often relies on outright impersonation without this level of sophistication.
So why is email spoofing so dangerous? It plays on our natural tendency to trust familiar names and brands. Unlike spam emails, which are usually filled with obvious red flags, spoofed messages are carefully crafted to blend into everyday communications.
In this guide, we'll take a closer look at the mechanics behind email spoofing and, more importantly, how to defend against it.
Why Is Email Spoofing Used?
Attackers use spoofed emails for various purposes, from financial fraud to large-scale disinformation campaigns. Let’s break down their common motivations.
Phishing Attacks: The #1 Goal of Spoofed Emails
Phishing is a type of email fraud where attackers try to trick you into sharing confidential information. They send emails that look like they're from well-known companies like banks, social media platforms, and even government agencies, and they urge you to click on a link or download an attachment.
For example, they might send you an email that looks like it's from an e-commerce platform you frequently use, asking you to "update your account details" because of some suspicious activity. If you click on it, you'll be taken to a fake login page designed to capture your credentials.
Spreading Malware and Ransomware
Some email spoofing attacks don’t ask for information – they deliver something much worse: malicious attachments or links to infected websites. These can install keyloggers, trojans, or ransomware, giving hackers control over the victim’s device or network.
Identity Theft
By pretending to be a trusted person – such as a CEO, coworker, or friend – attackers manipulate people into disclosing private information, transferring money, or making unauthorized changes to accounts.
Corporate Espionage and Cyber Warfare
If your organisation operates in a competitive industry, you need to be aware of the threat posed by email spoofing. Competitors or other interested parties may use this technique to get into your internal systems, steal your intellectual property or disrupt your operations. For example, a spoofed email sent to a research team could contain a Trojan horse designed to steal your proprietary data.
Personal Vendettas and Social Engineering Attacks
Not all spoofing attacks are financially motivated. Some are personal. Disgruntled employees, ex-partners, or even online trolls may use spoofed emails to spread false information, damage reputations, or harass individuals.
Email Spoofing vs. Phishing: Key Differences
Email spoofing and phishing are closely related, but they’re not the same thing. Let’s clear up the confusion.

Spoofing is a Technique, Phishing is a Goal
- Email Spoofing is when attackers fake an email sender's identity. It can be used for various attacks, including phishing, but it isn’t always tied to direct scams.
- Phishing is when attackers pretend to be trusted entities to steal sensitive information (passwords, financial details, etc.). Phishing almost always uses email spoofing as part of its strategy.
Spoofing as a Gateway to Phishing Attacks
While not every spoofed email is a phishing attempt, nearly every phishing attempt involves some level of spoofing. Here’s how:
🚨 Step 1: The Spoofed Email Lands in Your Inbox
- The email appears to come from a trusted source (e.g., "no-reply @amazon.com").
- It uses branding, logos, and official-looking content to seem authentic.
🎯 Step 2: The Hook – Creating Urgency or Fear
- “Your account has been compromised! Reset your password immediately.”
- “You have an unpaid invoice. Click here to avoid legal action.”
💀 Step 3: The Trap – A Fake Website or Malicious Attachment
- Clicking the link takes you to a fake login page created to steal credentials.
- Downloading an attachment infects your system with malware.
Not All Spoofed Emails Are Phishing Attempts
Some spoofed emails are used for other types of cyberattacks, such as:
- Spreading misinformation – Fake press releases or financial news to manipulate stock markets.
- Business Email Compromise (BEC) – CEO impersonation scams tricking employees into transferring money.
- Political cyberattacks – Disrupting elections or smearing reputations with forged messages.
How Is Email Spoofing Done?
Email spoofing might seem like a complex thing to do, but it's really just about taking advantage of known vulnerabilities within email protocols and infrastructure. To truly understand how spoofers do their attacks, let’s break down the technical mechanisms behind it.
SMTP Vulnerabilities: The Core Weakness
Email relies on Simple Mail Transfer Protocol (SMTP), a system designed in the 1980s – long before cybersecurity was a big concern. SMTP allows emails to be sent but doesn’t verify the sender's identity by default. This loophole means attackers can send messages that appear to come from any email address they choose.
One way attackers exploit this vulnerability is by finding unsecure email services with open SMTP ports. These open ports offer an easy way for attackers to launch spoofing campaigns.
Header Manipulation: Editing the “From” Field
Attackers modify the email header, which contains information about the sender, recipient, and other details, to display a false sender address. By altering fields like "Return-Path," "Reply-To," and "From," they can craft emails that appear legitimate at first glance.
Typosquatting: Creating Lookalike Domains
Some attackers register lookalike domains that mimic trusted websites, often using minor spelling differences or alternative top-level domains (TLDs).
Common typosquatting tricks include:
Email forwarding spoofing
Attackers can compromise an employee's email account and change the email forwarding rules. This allows them to intercept incoming messages and potentially gather sensitive information.
Tools and Technologies Used for Email Spoofing
Attackers use a variety of tools and technologies to carry out email spoofing attacks. Some of the common ones include:
- SMTP servers: Attackers may use their own SMTP servers or exploit open relay servers to send spoofed emails.
- Mailing software: Attackers use various mailing software, such as PHP Mailer (because it uses an open-source PHP library and is easily accessed), to send out large volumes of spoofed emails.
- Telnet: Telnet is a network protocol that allows users to connect to remote computers. Attackers can use Telnet to manually send emails with spoofed addresses.
- Spoofing tools: Various tools are available that can automate the process of email spoofing. These tools often allow attackers to forge email headers, generate fake sender addresses, and bypass weak email filters.
- AI-powered tools: With the rise of artificial intelligence (AI), attackers are increasingly using AI-powered tools to create more personalized spoofed emails. Lots of Gmail users have already been affected by AI-powered phishing attacks, and the level of sophistication makes it hard to tell the difference between real and fake emails.
Real-World Examples of Email Spoofing Attacks
Below are some real-life examples that illustrate the dangers of email spoofing and its far-reaching consequences.
- 2015: Mattel was tricked into sending $3 million to an account in China after an employee received a spoofed email that appeared to be from the CEO.
- 2018: A security researcher was able to spoof emails from a U.S. bank by exploiting a vulnerability in their email system. The researcher was able to send emails that appeared to be from the bank's CEO, which could have been used to trick employees into transferring funds or revealing sensitive information.
- 2018: The City of Ottawa was fooled into transferring $98,000 from taxpayer funds by an attacker claiming to be the city manager.
- 2024: Pepco Group, a major European retailer, lost around €15.5 million in a likely phishing attack that involved fraudsters spoofing legitimate employee emails to deceive the finance staff into transferring funds.
As you can see, even large organizations with presumably careful employees have been hit by email spoofing attacks. Now imagine how much more dangerous these threats can be to average, unprepared users who may not have the same level of awareness or access to advanced security tools. In the next section, we'll look at how to identify and protect against these attacks.
How to Identify Spoofed Emails

Email spoofing has become so sophisticated that even tech-savvy users can find it hard to tell the difference between fake and real emails. But there are some clear signs that can help you spot a spoofed message before it does you any harm. Let's look at them one by one.
1. Mismatched Sender Addresses
One of the biggest giveaways of email spoofing is a mismatched or slightly altered sender address. Cybercriminals often manipulate the "From" field to make the email appear as if it's coming from a trusted source.
🔍 Signs to watch for:
- The display name might look correct, but the actual email address is different.
- Subtle typos in domain names (e.g., @cornpany.com instead of @company.com).
- Emails that claim to be from internal company addresses but originate from an external domain.
2. Poor Grammar and Spelling Mistakes
While some spoofed emails are highly sophisticated, many contain spelling errors, awkward phrasing, or grammatical mistakes. Real companies and professionals rarely send poorly written emails.
🔍 Red flags:
- Misspelled words.
- Strange sentence structures or phrases that seem off.
- Generic greetings like “Dear Customer” instead of your name.
3. Urgent Calls to Action or Requests for Sensitive Information
Scammers rely on psychological manipulation to trick victims into acting quickly. Spoofed emails often ask for immediate action, creating a sense of panic.
🔍 Common phishing tactics:
- "Your account has been suspended. Click here to restore access."
- "Your payment failed! Update your billing details immediately."
- "Urgent: Security breach detected! Reset your password now."
4. Unfamiliar Links or Attachments
Just hover over links without clicking on them to see where they're going. If the link doesn't match what it says it is or if it shows you a website you don't recognize, don't click on it. And be wary of unexpected email attachments, especially ones with .exe, .zip or .doc extensions.
Studies have shown that many email providers allow forged emails to reach user inboxes despite having protocols to detect spoofing. Some providers use visual security cues on unverified emails, but these cues aren't always effective at preventing users from falling for spoofing attacks.
So, you need to be careful yourself, especially if you use traditional email providers, not secure ones, as they may lack the advanced safeguards needed to protect against sophisticated spoofing techniques.
How to Protect Against Email Spoofing
Email spoofing prevention requires a multi-layered approach that combines technical measures, security awareness, and vigilance. Here's a breakdown of key strategies.
Analyze Email Headers for Authenticity
Analyzing email headers provides deeper insight into the origins of a message. Email headers contain metadata about the email's journey from sender to recipient, including server routes and authentication records. Here’s how to interpret them:
- Check the "From" Field vs. "Reply-To" Fields. Discrepancies may indicate spoofing. For instance, an email appearing to come from info @legitcompany.com might have a Return-Path pointing to fraud @example.com.
For example, in Gmail it’s here:

Use Email Aliases to Reduce Exposure
One simple but powerful way to protect your primary email address is by using email aliases.
🔍 What are email aliases?
- Alternative email addresses that forward to your main inbox.
- Can be used for different services (e.g., banking @yourdomain.com, newsletters @yourdomain.com).
- Reduce exposure of your real email, making it harder for attackers to target you.
Instead of giving your real email when signing up for websites, use disposable aliases. If an alias gets compromised, you can disable it without affecting your main account.
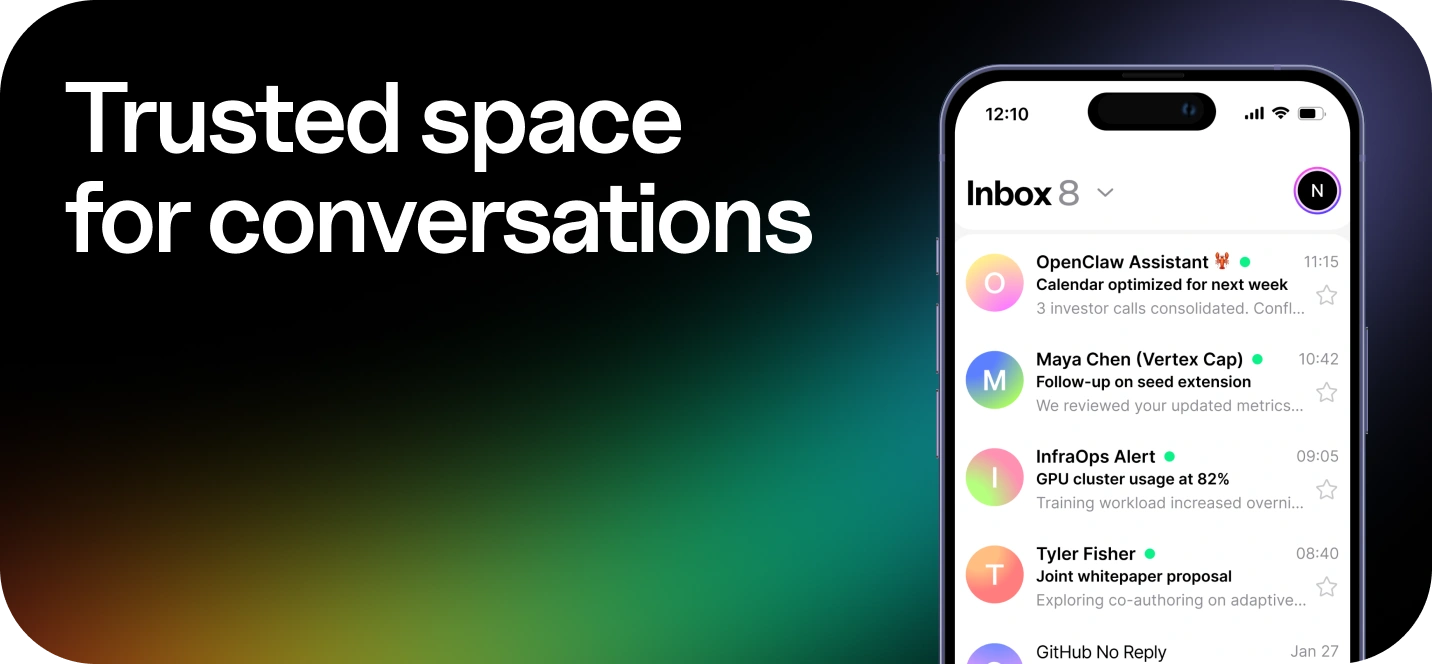
Use Secure Email Services
Using a secure email service is one of the most effective ways to protect against email spoofing. Traditional email providers often lack the necessary safeguards, allowing attackers to take advantage of vulnerabilities such as unsecured SMTP ports. Secure email services, like Atomic Mail, address these weaknesses with advanced security features:
- Email Authentication Protocols: Secure services support SPF, DKIM, and DMARC to verify sender authenticity and prevent tampering during transit. Proper configuration of these protocols is critical in stopping spoofing attempts.
- Advanced Filtering: These platforms use advanced filters to detect and block spoofed emails, spam, and malware by analyzing sender details, content, and attachments for potential threats.
- Encryption: Secure email services use end-to-end encryption to protect sensitive data, making it impossible for attackers to intercept and steal information.
- Trusted SMTP Servers: Secure email services rely on trusted SMTP servers with modern security measures to ensure emails are sent only from authenticated sources.
By leveraging these features, secure email services provide robust protection against email spoofing and related cyber threats, safeguarding both personal and business communications.
Exercise Caution and Vigilance
- Verify sender information: Always double-check the sender's email address for any discrepancies. Be wary of emails from unknown senders or emails that look suspicious.
- Be cautious with email attachments and links: Avoid opening attachments or clicking on links in unsolicited emails, especially from unknown senders.
- Be skeptical of requests for information: Real organizations typically don't request sensitive information like passwords or bank details via email.
- Report suspicious emails: If you receive a spoofed email, report it to your email provider or IT department.
Implement SPF, DKIM, and DMARC for Domain Protection
For domain owners, one of the most effective ways to prevent email spoofing is using email authentication protocols. These security measures verify whether an email actually comes from the sender it claims to be from.
- SPF (Sender Policy Framework): SPF lets you say which mail servers can send emails on your domain. This stops spammers using your domain to send emails without your permission.
- DKIM (DomainKeys Identified Mail): DKIM is great for making sure that emails haven't been tampered with when they're being sent. It adds a digital signature to outgoing emails, so the person receiving the email can check that it was sent by the right person and not someone else.
- DMARC (Domain-based Message Authentication, Reporting, and Conformance): DMARC is based on SPF and DKIM, and it lets you set out how mail servers should deal with emails that haven't passed SPF or DKIM authentication. DMARC also provides reporting mechanisms that allow domain owners to monitor email authentication results and identify potential spoofing attempts.
⚙️ Setting up SPF, DKIM, and DMARC ensures that your domain can’t be used for email spoofing.
Conclusion
Email spoofing is a widespread cybersecurity issue that affects individuals, businesses, and organizations worldwide. As attacks become more sophisticated, relying on outdated email security measures is no longer an option.
Key Takeaways:
- Email spoofing is a growing cyber threat – Attackers manipulate email headers and domains to impersonate trusted senders.
- Spoofing is often a gateway to phishing attacks, malware distribution, and other cybercrimes.
- Red flags like mismatched sender addresses, poor grammar, and urgent requests can help you identify spoofed emails.
- The best protection is proactive defense – Using a secure email provider with built-in anti-spoofing features eliminates risks at the source.
💡 Why Choose Atomic Mail?
Atomic Mail is an encrypted email service which provides the highest level of email security, ensuring that your emails remain private and resistant to modern cyber threats:
- End-to-End Encryption: Ensures your emails remain private and tamper-proof.
- Advanced Filters: Detect and block spoofed emails, spam, and malware by analyzing sender details, content, and attachments for potential threats.
- Free Email Aliases: Create multiple email aliases to protect your primary email address and reduce the risk of exposure to phishing or spoofing attempts.
- User-Friendly Interface: Designed for both individuals and businesses, Atomic Mail makes it easy to stay secure without compromising convenience.
- Private by design: No tracking, no data collection, no surveillance.
🔗 Sign up for Atomic Mail now and experience the future of secure email communication!